

Rs 4860 only/-
9907385555 asingh039@gmail.com
MP NAGAR BHOPAL
INTRODUCTION
Image mining is the way toward looking and finding profitable data and information in vast volumes of information. A portion of the techniques used to assemble information are, Image Retrieval, Data Mining, Image Processing and Artificial Intelligence. These strategies permit Image Mining to have two diverse methodologies. One is to separate from databases or accumulations of Images and the other is to mine a mix of related alphanumeric information and accumulations of Images. In design acknowledgment and in Image handling, feature extraction is a unique type of dimensionality lessening. At the point when the information is too expansive to be in that point the information will be changed into a decreased portrayal set of features. Feature extraction includes disentangling the measure of assets required to portray a huge arrangement of information precisely. A few features are utilized as a part of the Image Retrieval framework. The well known among them are Color features, Texture features and Shape features.
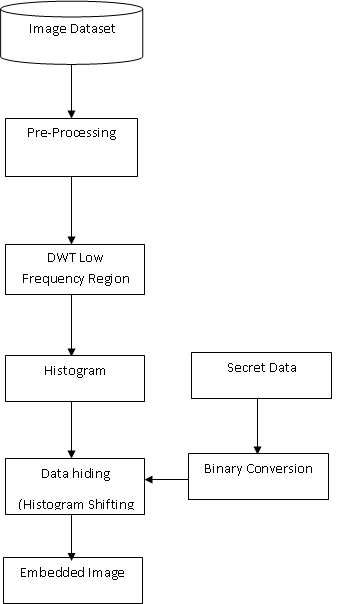
Proposed Work
Text Pre-Processing: Text preprocessing is comprising of words which are in charge of bringing down the execution of learning models. Information preprocessing lessens the span of the info content inquiry altogether. Stop-words are useful words which happen much of the time in the dialect of the content (for instance a, the, an, of and so on in English dialect), with the goal that they are not helpful for arrangement.
Conclusions
In the exploration of Image recovery, there are a great deal of accomplishments in picture semantic feature, they can be connected to content-based picture recovery to examine the move between visual elements and semantic elements of the pictures. This paper uses the new blend of textual and also visual components for positioning the picture as both make the re-positioning procedure all the more capable, which is appeared in results. Here it is demonstrated that utilization of single element reduces the accuracy of the work, so multiple feature can increase the accuracy as done in this work. In future one can opt other feature combination with encryption for data security as well.
| IEEE Base paper | |||
| Doc | Complete Project word file document | ||
| Source Code | Complete Code files |